Two fairly recent events should have erased all doubt about whether cyberattacks are a serious threat to critical infrastructure, including water and wastewater treatment plants.
In February, an attack on a water treatment facility in Oldsmar, Florida, briefly but dramatically changed the level of sodium hydroxide in the water. If the operations team had not detected the change and taken action, the sodium hydroxide in the water supply would have reached an extremely dangerous level.
In May, a ransomware attack on the largest fuel pipeline serving the East Coast of the United States forced a temporary shutdown of operations and led to gasoline shortages in multiple states.
These should not be seen as isolated incidents, as cybercrime is on the rise worldwide.
Schneider Electric is among companies carefully monitoring trends in cyberattacks and advising water and wastewater utilities on how they can defend themselves. Andrew Nix, an operational cybersecurity consultant with the company, talked about the issues and the path to cyber-confidence in an interview with Treatment Plant Operator.
How widespread is the threat of cybercrime today?
Nix: Cybercrime and cyber incidents on the operational side are a hugely growing issue with critical infrastructure and with public and private organizations both private and public. The U.S. Department of Justice estimates that cybercrime will cost the global economy $6 trillion this year, more than the gross domestic product of the United Kingdom and France combined.
What does the picture look like on the industrial and utility side specifically?
Nix: In 2016 the Industrial Control Systems Cyber Emergency Response Team, a division of the Department of Homeland Security, qualified 390 new vulnerabilities in the industrial control space that could affect critical infrastructure including water and wastewater utilities. Of those, 91% were classed as vulnerabilities susceptible to remote attack. Accenture, a major consulting firm, has estimated that operational cyberattacks have gone up by more than 67% since then.
Why are attacks on the operational side so worrisome?
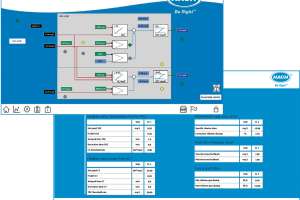
Nix: In the operational technology space it can be hard to quantify how many attacks there are because most organizations have little visibility to the day-to-day happenings of their operational systems — their SCADA and control systems. So they don’t find out about intrusions until weeks or even months after they happen. By then the damage may already be done. The information has been leaked, they’re in panic mode trying to get it resolved, they don’t necessarily know where it started, and so they can’t definitively say it won’t happen again.
What is the greatest type of risk for entities like water and wastewater utilities?
Nix: Downtime to operational systems is the number one driver behind cybersecurity risk in that space. The water industry has huge potential for life safety implications if there is a failure in delivery, in purification, in any number of things. Water is the basis of human life, and delivering it in a timely and safe manner is absolutely critical.
What lessons can be learned from the attack on the Florida water plant this year?
Nix: Very few utilities are exempt from similar events. The attack could have happened to anyone. An unknown person somewhere in the world gained full read and write access the facility’s SCADA system. Fortunately, the value in question was changed so dramatically that an employee noticed it and was able to shift it back and raise an alarm. But imagine if that happened during a shift change, in a hurricane, or at three in the morning. Attackers don’t work on your schedule. They don’t care if you’re short-staffed, if you haven’t had time to patch your PLCs, or if there wasn’t budget for cybersecurity this year. They will take advantage of that.
What exactly do you mean in talking about the path to cyber confidence?
Nix: It’s about what can be done for the people who deliver clean water and deliver the energy that keeps our society running and keeps us comfortable and happy in our homes. It’s about giving them the ability to go home at night feeling that their operation is safe. That comes down for key areas: Reliance on standards, effective training and enforcement of a cybersecurity culture, observing cybersecurity fundamentals (see sidebar), and being unafraid to ask for help.
What are these standards and in what ways are they helpful?
Nix: There are standards like IEC 62443, and there are AWWA standards. The AWWA cyber risk tool can give high-level guidance to what cyber policies and procedures a utility needs to have in place in order to run facilities safely. Tools like that provide great starting points, but there’s a need to understand how they apply to a particular industry and a particular facility.
How does training fit into the picture?
Nix: In training and enforcing a culture of cybersecurity, it’s important for everyone in the organization to know how they, in their specific roles, fit into being cybersecure. That means going beyond a mandated minimum of training to implement a role-based cybersecurity workshop. Those operating the SCADA system, for example, need to understand the impact they have on the cybersecurity hygiene of the facility, versus someone operating an engineering workstation or someone on the administrative side. People in each role need to have a genuine feel for how they fit into the cyber health of the organization and what their responsibilities are in keeping it safe.
Why is it important for water and wastewater utilities to reach out for assistance?
Nix: Their core business is delivering safe drinking water or cleaning wastewater and making sure they meet the necessary standards. They shouldn’t have to be cybersecurity experts in their own right. It’s appropriate for them to reach out and ask experts in the cybersecurity field for assistance. That way the folks they hired can focus on making their facilities runs flawlessly, while experts help make sure the cybersecurity of the equipment is stable and up to date.
What kinds of assistance can a firm like yours provide?
Nix: We have the perspective of not only manufacturing equipment that runs water and wastewater facilities, but also operating manufacturing facilities of our own that we have to protect from a cybersecurity standpoint. So we have strong insights into the ways many industries manage cybersecurity, and can help our customers secure their operational infrastructure as well. We’ve developed a team of cybersecurity consultants who can help water and wastewater entities understand the level of cybersecurity they need to defend against the latest threats in their industry.
How would you define the level of security water and wastewater facilities need?
Nix: The standards specify security levels from 1 to 4. Given the criticality of water, we recommend that water and wastewater organizations aim for Security Level 3, which is protection against intentional violation using sophisticated means with resources. We can help customers identify where they stand today, what their risks are, and where the gaps are in their current system. Then we can help them pick the most cost-effective way to make themselves an unattractive target for cybersecurity bad actors.